We all use apps. A lot. There are over 2 million to choose from on the Apple and Google Play app stores. The average person spends more than two hours a day on apps and uses 30 apps each month.
That’s a lot of time. And a lot of data. But not the kind your mobile carrier tracks. We often think about how mobile apps affect our social connections or productivity, we don’t always think about how these phone apps can impact cybersecurity when we’re at work, but they can.
Because many workplaces are “BYOD” (bring your own device), the line between personal and workplace use is blurred. If an app you downloaded at home is compromised, now your company data is at risk as well.
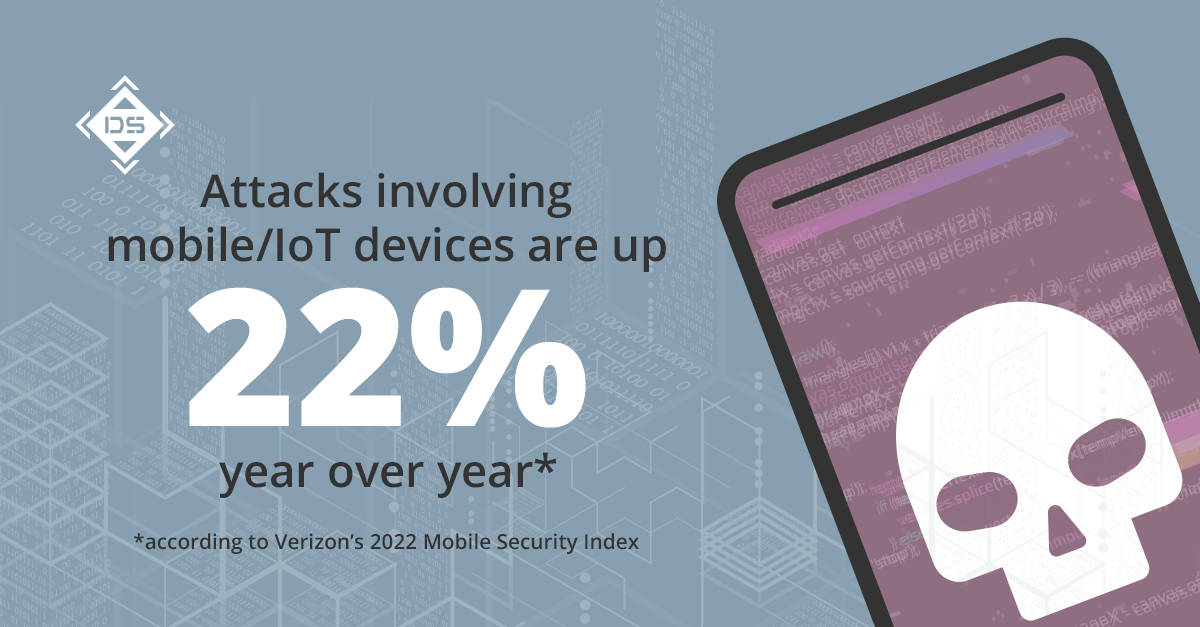
Data shows app vulnerability is on the rise. Major attacks involving mobile or Internet of Things devices are up 22% year over year, according to Verizon’s 2022 Mobile Security Index, an independent survey of 632 security professionals who manage mobile and IoT devices for their companies.
Other findings from the study:
- 85% of companies surveyed have a budget dedicated to mobile security, yet 45% of companies suffered a compromise involving a mobile or IoT device in the past 12 months
- 79% of respondents agreed that recent changes to working practices, such as always-on call or hybrid schedules, have adversely affected their organization’s cybersecurity
- 85% said home Wi-Fi and cellular networks/hotspots are allowed or there is no policy against them, and 68% allow or have no policy against the use of public Wi-Fi.
- 52% of respondents said they have previously sacrificed the security of mobile devices, including IoT devices, to meet a deadline or hit productivity targets
Taking inventory of your apps
If you think about cybersecurity like protecting your house, you’d lock up everything you know about, such as doors, windows, etc. But you can’t lock something you don’t know exists. That’s why understanding what apps and cloud services touch your ecosystem and how they impact your security is the start of a well-rounded security strategy.
Threat actors have been known to leverage apps and services that you aren’t paying attention to. Let’s say an employee decides that they want to leverage a cloud service/app for manipulating data. The output is something they download and add to their work deliverable, but the initial data is left in the app. If an employee leaves, or worse their credentials are stolen the threat actor might be able to leverage that information against your organization.
Sounds far fetched? There are articles written about the use of code repos and keeping your secret keys secret.
One of the big things we see in the major hacks is that the threat actors are hanging out in the system for a while before they actually do anything and before anyone realizes it.
In addition to checking the permission settings on your apps and or services, it’s also important to know who the developer is. And also consider that apps offered on the main Apple and Google platforms might have data privacy issues as well.
TikTok, for example, is making headlines because the U.S. House of Representatives, the military and several states have banned the use of the app on government devices because of the concern that China, where TikTok’s parent company ByteDance is located, could access American citizens’ personal — or in this case, government — data. And many other popular apps collect your personal information as well.
Pay attention to small business apps as well
It’s not just Fortune 500 companies putting out apps. In a survey of 1,000 small business owners, nearly half (48%) said they have an app and one in four said they planned to launch one in the near future.
Small businesses are building apps to connect with customers but some of them unintentionally have security gaps. Also, consider the privacy of the data you transfer to small businesses through these apps. While the app itself might not get hacked, is the business well-staffed to protect your data once it’s in their hands?
According to that same survey, 79% outsource their app development either to a team or a freelancer and 43% use DIY software.
How Digital Silence can help
Digital Silence’ Application Security experts make sure apps don’t create pathways to your, or your company’s, confidential data. We use a proprietary app-testing methodology that examines the information your apps may be exposing as well as examines the underlying cloud environment, letting you know of potential risks.